Public Key Cryptography is like a small miracle: two people out in complete public can each shout out their public keys for the whole world to hear and somehow end up with a secure encryption key which only those two can generate. The problem comes when they lose the ability to communicate in public.
Imagine instead of shouting, they each mail their public key through the UPS. Before delivering the message, the UPS opens both letters, reads them, and then sends out a dummy copy while hiding the originals. These fabricated letters use a public key from the UPS so that when Alice and Bob receive the letters, they both encrypt their messages so UPS can read it.
This is called a man-in-the-middle (MITM) attack — UPS can get away with it because they can forward the messages and have tricked each participant into thinking the UPS public key is the public key of their intended recipient. UPS gains the power to impersonate and place themselves between any two parties they relay messages to. They can read and modify messages invisibly.
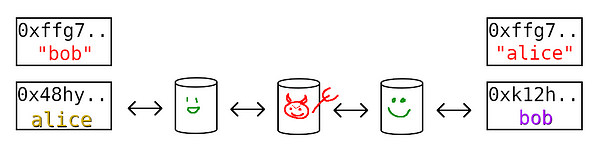
In reality a MITM attack takes place over the internet, but the same principle applies. Alice and Bob don’t end up with each other’s keys, but with Eve’s key (red). Since they haven’t authorized each other yet and they rely on these relays, they can never be sure that they have received genuine identification from the other party.
The Web 2 Solution
Obviously some solution exists — the internet as a whole is clearly vulnerable to the same attack, likely more so considering all the parties involved in relaying data — and one does: Public Key Infrastructures (PKI) solve this problem for us. Rather than dive right in to what is explicitly referred to as a PKI, it’s intuitive to use an example of a service which implicitly behaves as such to see how it helps solve the MITM attack.
Facebook solves the MITM attack for its users (so long as they trust Facebook). Say you want to use your public key to connect over the internet with someone from your hometown by combining with their public key. If either of you just sent that public key to some arbitrary server each other could access, you would be giving every relay along the way the chance to modify the message to replace in its public key rather than yours.
So rather than allowing those nodes you rely on to send the message to impersonate you, you each decide to *trust* Facebook. You register your public keys with Facebook, and when you want to connect with your friend, you ask Facebook what their public key is (this isn’t exactly how Facebook works, but it’s close enough and makes a simple example). Now when those pesky relays attempt to swap out the public key before it reaches your friend, Facebook can check the key they received against their keys on record.
Any relay attempting a MITM attack is thwarted when Facebook rejects those messages with the wrong public key. But what if Facebook wanted to MITM attack you? They would simply tell you and your friend the wrong public key — their public key, and we’re back at square one. Yet this is the security you get from Facebook, from all Web 2 services; you implicitly trust the website you use to intermediate communications to prevent MITM attacks and refrain from doing it themselves.
The Real World
And this, on a small scale, is the nature of PKIs. If you trust them, and they behave faithfully, they serve as a sort of referee which prevents MITM attacks. What most people refer to as PKIs actually do not offer this service to individuals, but to the websites themselves — protecting users from connecting to fake websites posing as the real thing. And, again, they are secured by trust. Their size and the scrutiny on them makes them fairly secure — secure enough to give us the modern internet, but they are known targets for hacks and government corruption.
And even granting large scale PKIs the benefit of the doubt, most people online don’t benefit from them when connecting to other people. These large PKIs which secure the web browser can’t possibly register every person and user account — that’s delegated to websites like Facebook. So whatever the security of the PKI which tells you Facebook.com is legit — you still ultimately rely on Facebook, or whatever website, to prevent MITM attacks and refrain from performing them themselves.
If governments can compromise the large scale PKIs, what hope do these companies have? Even if you rely on some charismatic leader to fight outside interference, you can never know that they themselves aren’t taking advantage. In practice, these websites keep as much of their protocols as possible hidden and make users reliant on them — they don’t need to MITM attack because users have already conceded so much freedom and privacy — their recourse otherwise isn’t much better.
While most people think of the service a website provides as their servers, their user experience, the features — perhaps the most important service Web 2 companies provide is their promise that you are cryptographically secure. The ability to secretly compromise that assurance at their discretion is the price you pay, and you can be reasonably sure they won’t let any outside parties MITM attack because, well, knowledge is power — and they are accumulating.
A Universal Medium
The wrinkle which makes a MITM attack possible is that someone can alter and replace a message in transit without being detected. Consider that instead of sending messages through relays, everyone bought powerful telescopes and laser beams and instead shined their messages on the moon. Ignoring the logistical and practical failures of this: in theory, there would be a shared medium which could not be censored.
Any uncensorable shared medium which everyone could access would work to prevent the MITM attack without trusting in any middleman. Much like shouting in public, if someone attempts to mimic the person shouting a public key to you, you will obviously be able to detect that you heard it twice and something is fishy. You connect to both public keys and can quickly figure out which is real when the legitimate one (the one not sitting between you and your partner) and yourself discover you are each also connected to a stranger on the other channel.
It’s important to note that a PKI alone cannot prevent impersonations: someone with a public key claiming to be a person who they are not. It’s just that when you search for someone it will show all the people claiming that identity, while a MITM attacker censors all but their own fake identity. When all key exchanges are posted for all to see, it becomes clear which ones have attackers inserted in the middle and which do not.
The Web 3 Solution
A universal medium works as a PKI which doesn’t force you to place trust in anyone, but obviously something more practical than shining lasers on the moon is required. Enter blockchain. Blockchain is significant because it introduces costs to modifying, censoring and altering data. It, in the best case, is a medium which allows anyone to publish data and earn rewards onto a medium whose cost to alter grows as data becomes older and older. It is evermore costly to censor and modify and anyone can take up its duties for reward.
It’s perfect — except for… well, the cost. Exchanging public keys is too common an activity to be paying the fees of blockchain to perform; in practice the economics don’t make sense — the cost of trusting a middleman is preferred to the cost of doing all key exchange on a traditional blockchain. While blockchain of the past may be good at racking up a cost for modifications to the chain or spurious creation of new chains — it is not good at managing its own economics.
As demand grows, fees grow, and the fees don’t pay for the infrastructure, which could increase the supply and keep costs constant or even reduce them (like a normal business). As the chain grows, the data burden grows too — and since blockchain doesn’t know how to remove data, it grows arbitrarily forever. Neither of these ailments will ever allow a blockchain to handle the global traffic which trustlessly prevents MITM attacks for the entire globe. At least, not any traditional blockchain.
Saito
And so in steps Saito. Two fundamental innovations each worthy of their own books will only be mentioned here: routing work based rewards fund infrastructure which actually runs the network while heavily punishing censorship and delays, and automatic transaction rebroadcasting instantiates a fair and economically sound protocol for data pay its genuine market-determined storage costs and be removed otherwise.
Since the chain can’t grow forever without receiving funding, and rewards go towards network infrastructure, the chain can grow without simply raising costs as new users show up or time goes by. It can keep transaction fees steady as it grows to meet global demand. It can serve as a PKI network accessible to anyone at a fair, low cost — a universal and uncensorable medium to secure global communication without relying on archaic trust assumptions.
The refereeing that Web 2 companies like Facebook had to be trusted to perform can now be done by users themselves — no trust required. Because the network rewards nodes for routing around censorious relays, it incentivizes data to flow where it is needed. Anyone launching a MITM attack must fight the rest of the network to prevent them from revealing their attempt.
There is a sense in which any blockchain could do this — any chain which is a universal medium. But without the ability to scale for global use it will be a flash in the pan — and Saito being the only network which rewards efficient routing, is also the only network which actively fights against censorship of block data both to and from users. In extreme attack scenarios where a user can only connect to one node, Merkle Completeness Proofs can thwart selective lite-block censorship.
It’s not just that blockchain has never been able to scale — network security, PKI, has never been able to scale either: relying on Facebook and other delegated companies to serve as middleman who prevent MITM attacks only when they feel like it is not a solution. The large scale PKIs are built with the same trust assumptions, but they can’t even grant that limited accountability to the individual — the individual gets PKIs set up by companies whose primary objective is to monetize their personal information — the opposite of cryptographic security.
These companies use every chance they get to spy and surveil us — they would surely sell the ability to MITM to the highest paying government agency, and they are in a constant battle against hackers seeking to steal that privilege. Imagine what is possible on the internet when we no longer require that every website also serve as a fortress — when we can all rely on a trustless and low cost medium capable of driving the most well funded attackers broke and dysfunctional.
The strangleholds, the monopolies, the abuse of trust. The internet is not free until individuals are secure. Users who are forced to trust the biggest players for protection are not free. Saito is freedom.
Talking Turkey
It would be easy and warranted to say that Saito is the most fundamental solution to a problem, the MITM attack, which requires an industry projected to be worth $20 billion in the next ten years — and call it a day.
But that’s too conservative. What PKI means to most people in the industry does not include the delegated authorizations that social media uses to secure users from MITM attacks — the term is usually just reserved for websites. Saito isn’t just capable of replacing the big boys, it’s capable of seeping in between the cracks all the way down to interpersonal peer-to-peer communications.
Where traditional Web 2 PKI fails and concedes to trust assumptions from begrudging and untrustworthy corporations, Saito grants economic security more efficient and robust than Bitcoin — without the limiting costs on users.
The entire division of social media companies responsible for user security can be easily outsourced to the Saito Network — it will remove trust, be safer cheaper and give users freedom from digital monopolies. The value of that is difficult to estimate but far greater.
It makes the theoretical implications of Saito for internet security and privacy far more profound than just revolutionizing a $20 bn industry — Saito is the completion of public key cryptography, and it revolutionizes and dis-intermediates the entire internet.
It can only achieve this because it is the first blockchain which can fund its own means — thus forcing nodes to compete to keep costs as low as possible.
It is a revolution in both blockchain and internet architecture; at the time of writing, Saito’s market capitalization is $16 million.
Further Reading:
The Case for Fewer Chains
A common question for those investigating a new blockchain is: what are the use cases? Money, smart contracts…
medium.com
Saito Wiki
Documentation and Community information for the Saito Project
wiki.saito.io
muk's Newsletter | Substack
Easier than hosting a blog. Click to read muk's Newsletter, a Substack publication. Launched a year ago.
mukdde.substack.com






















































